Table of Contents
Picture this: encryption acts like an impenetrable lockbox for your data. It ensures that even if someone intercepts your messages, gains unauthorized access to your files, or breaches your website, they won’t be able to make sense of the jumbled mess they find. This is crucial in an age where cyberattacks are a constant threat.
Whether you’re a concerned individual, a business owner protecting customer data, or a website owner safeguarding user information, understanding encryption is paramount. Think of it as the cornerstone of your digital defense strategy.
The Importance of Encryption for WordPress Websites
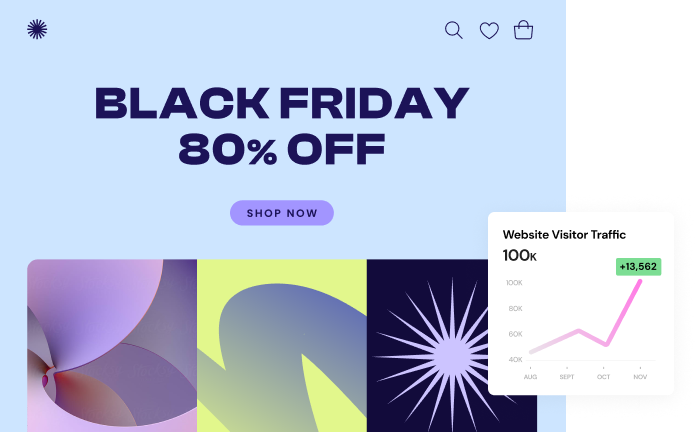
WordPress, the world’s most popular website builder–powering millions of websites–is a treasure trove of potentially sensitive data. This includes customer information, login credentials, financial details, and even the site’s content itself. That makes WordPress websites a prime target for hackers. Encryption, combined with specialized WordPress hosting like Elementor Hosting, offers a robust shield for your site.
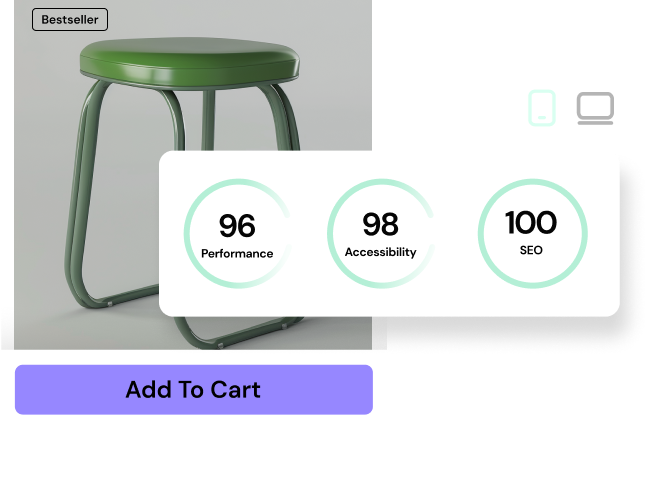
With Elementor, you not only get the visual design power to build stunning and secure websites easily, but you also benefit from a hosting environment specifically optimized for WordPress. This includes cutting-edge encryption technologies, advanced security features, and lightning-fast performance – all designed to protect your data while ensuring a seamless user experience.
In the following sections, we’ll delve into these concepts:
- The basics of how encryption works
- Different types of encryption used in everyday applications
- Essential best practices to safeguard your data
- How to leverage Elementor and its hosting platform to maximize the security of your WordPress website.
Encryption Fundamentals
Plaintext vs. Ciphertext
At the heart of encryption lies a simple concept: transforming readable information (known as plaintext) into a scrambled, unreadable format (called ciphertext). Think of plaintext as your original message, a sensitive document, or a password. The encryption process takes this plaintext and applies a complex mathematical formula (called a cipher) along with a secret key. This jumbled output is your ciphertext – it might look like a meaningless string of letters, numbers, and symbols.
Only those in possession of the correct key can reverse the process, decrypting the ciphertext back into the original, human-readable plaintext. With the key, the ciphertext remains a manageable puzzle, shielding your confidential data from prying eyes.
Encryption Algorithms
Encryption algorithms are the backbone of the entire process. They’re the mathematical recipes that dictate how to transform your data and create a strong cipher. There are two main categories:
- Symmetric Encryption: This type uses the same secret key for both encryption and decryption. Imagine you and a friend share a lockbox with a single key that both of you have. Well-known examples include AES (Advanced Encryption Standard), DES (Data Encryption Standard), and Twofish.
- Asymmetric Encryption: This method employs a pair of keys. One key, the public key, encrypts data. The other, the private key, is needed to decrypt it. It’s like having a mailbox where anyone can drop letters (encrypted with the public key), but only you have the key to open it and read the contents (decrypt with the private key). RSA and Elliptic Curve Cryptography (ECC) are widely used asymmetric algorithms.
Key Length: The Backbone of Encryption Strength
Key length, measured in bits, is critical to encryption security. A longer key means exponentially more possible combinations, making it harder for attackers to crack the code through brute force. Think of a bicycle lock: a 3-digit combination is easier to guess than a 10-digit lock. Modern encryption standards typically use keys ranging from 128 to 256 bits.
Hashing for Data Integrity
While encryption is about confidentiality, hashing is all about ensuring that your data has not been tampered with. A hashing function takes an input of any size (a password, a document, even an entire software program) and produces a unique, fixed-length output called a “hash” or “digest.” Think of it as a digital fingerprint for your data.
Here’s where it gets interesting:
- One-way: Hashing is a one-way function. You can easily compute a hash from the original data, but it’s virtually impossible to reverse the process back to the original input.
- Sensitive to Change: Even the tiniest change to the original data will result in a completely different hash value, making it ideal for detecting tampering.
- Common Hashing Algorithms: Popular examples include the SHA family (SHA-1, SHA-256, SHA-3) and MD5 (although MD5 is now considered vulnerable for some use cases due to the discovery of collisions).
How Hashing Works in the Real World
- Password Storage: When you create a password on a website, responsible services should never store the password itself. Instead, they run it through a hashing function (often with additional techniques like salting, explained later) and store the hash. When you log in, they hash the password you enter and compare it with the stored hash, granting you access if they match.
- Verifying File Integrity: Many software downloads offer hash values alongside the files. You can calculate the hash of your downloaded file and compare it to the provided value. A match confirms the file hasn’t been corrupted or altered in transit.
- Data Integrity Checks: Databases and systems sometimes use hashing to ensure data remains unchanged.
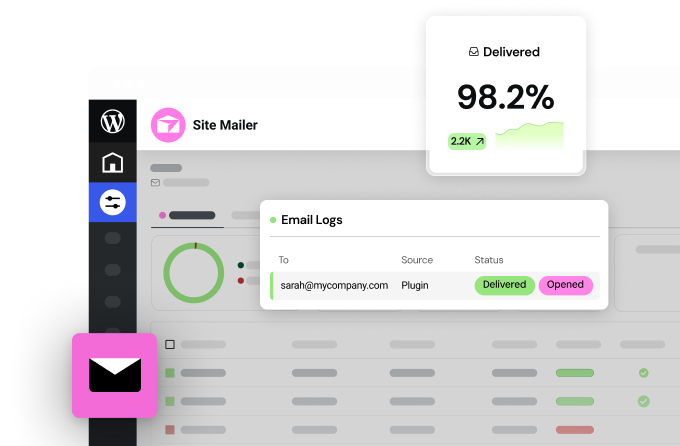
Hashing and Elementor
Elementor takes password security seriously. When you create an account, Elementor doesn’t store your password in plain text. It uses a strong hashing algorithm along with techniques like “salting” (adding unique data to each password before hashing) to make it incredibly difficult for attackers to decipher passwords, even if they were to compromise a database.
Cryptographic Keys
Think of cryptographic keys as the heart of encryption. They dictate the specific way the cipher transforms your data, making it unreadable without the correct key. Let’s break it down:
- Symmetric Keys: As you recall, symmetric encryption uses the same key for both encrypting and decrypting data. This means that securely sharing that key between authorized parties is crucial.
- Asymmetric Keys: With asymmetric encryption, there’s the public key (which anyone can use to encrypt data) and the all-important private key (known only to the intended recipient for decryption). Protecting your private key is paramount for maintaining the security of the whole system.
- Key Exchange: In scenarios where you need to use symmetric encryption, how do you safely share the secret key with the other person? This is where key exchange mechanisms come into play. Popular methods like Diffie-Hellman key exchange allow two parties to establish a shared secret key over an insecure communication channel.
Secure Key Storage Practices
Since keys are the linchpin of encryption, safeguarding them is absolutely essential. Here are a few best practices:
- Strong Key Generation: Use random, unpredictable keys of the appropriate length. Avoid predictable patterns derived from personal information.
- Hardware Security Modules (HSMs) are specialized devices designed to generate, store, and manage keys securely. Enterprises that handle highly sensitive data often use HSMs.
- Password Managers: For individual users, a reputable password manager can aid in generating and storing strong encryption keys.
- Limited Access: Based on the principle of least privilege, minimize the number of people with access to encryption keys.
Keys in Website Security
HTTPS websites, essential for safe browsing, rely on digital certificates. These certificates contain public keys used to establish encrypted connections between your browser and the website you’re visiting. Behind the scenes, key exchange mechanisms help your browser and the website agree on a shared key for encrypting the data flowing between them.
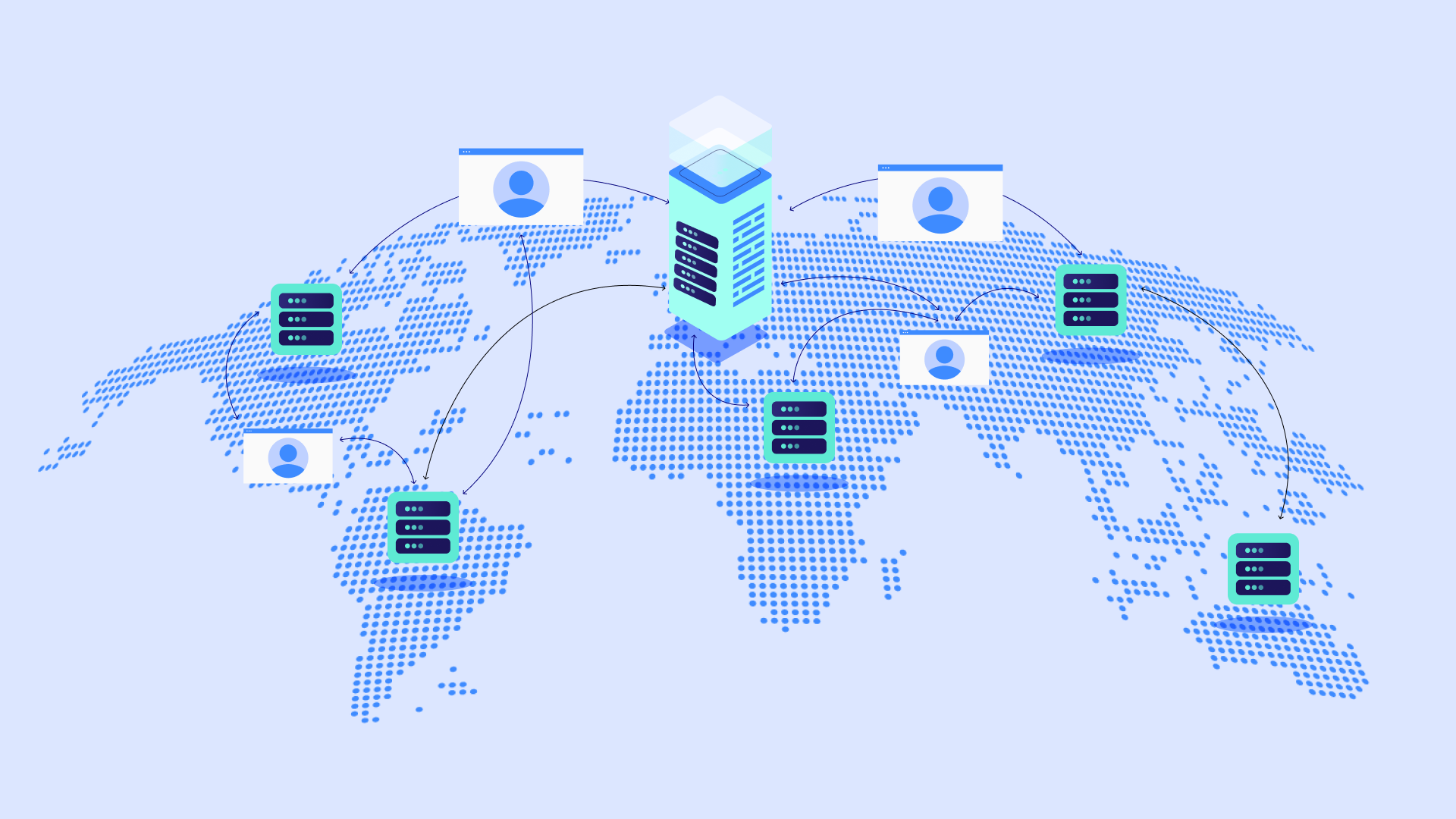
Elementor’s Focus on Security
Elementor Hosting prioritizes your website’s security. With infrastructure built upon the Google Cloud Platform and a partnership with Cloudflare, Elementor ensures industry-leading security practices to protect your website’s data. This includes robust key management and security measures aligned with international standards.
How Encryption Works: A Deeper Look
Mathematical Ciphers
At their core, encryption algorithms are intricate mathematical formulas. Let’s briefly revisit some historical concepts to understand the foundations of modern encryption:
- Substitution Ciphers: These simple ciphers replace letters in the plaintext with different letters according to a predefined rule. For example, the Caesar Cipher shifts each letter by a fixed number of places in the alphabet.
- Transposition Ciphers: Here, the order of the letters in the plaintext is rearranged following a specific pattern.
While these historical ciphers were vulnerable to cracking, they laid the groundwork for much more complex and secure methods.
Modern Block & Stream Ciphers
Modern encryption algorithms fall broadly into two categories:
- Block Ciphers: They operate on fixed-sized blocks of data. Popular examples, like the Advanced Encryption Standard (AES), process data in 128-bit chunks, applying complex transformations multiple times (often in “rounds”).
- Stream Ciphers: These encrypt data one bit or one byte at a time, making them suitable for real-time applications where speed is critical. However, they can be more susceptible to certain types of attacks.
Harnessing the Power of Modes of Operation
Block ciphers alone aren’t enough. Modes of operation determine how they’re applied to handle data larger than a single block:
- Cipher Block Chaining (CBC): Each block’s encryption depends on the previous one, which helps propagate changes throughout the ciphertext.
- Galois/Counter Mode (GCM): Faster and more parallelizable than CBC, GCM also provides built-in authentication, helping to verify data integrity.
Other modes of operation exist, each with its strengths and weaknesses. The choice often depends on specific security needs and performance requirements.
The Encryption Process
1. Choosing the Algorithm & Key: The first step involves selecting an appropriate encryption algorithm (e.g., AES, RSA) and generating a corresponding key. Key length will be determined by the chosen algorithm and desired security level.
2. Preparing the Plaintext: Your data—a text message, a document, an email—is the plaintext input into the encryption process. Depending on the algorithm, it may be divided into blocks.
3. The Magic of Transformation: Here’s where the cipher comes in. The algorithm, guided by the key, performs a series of complex mathematical operations on the plaintext. This includes substitutions, permutations, bitwise operations, and more. The specific algorithm dictates the exact steps.
4. Output: Ciphertext: This seemingly random, scrambled output is your ciphertext. It bears no resemblance to the original message and is essentially unreadable without the correct key.
Illustrative Example (Simplified!)
Imagine a very simple substitution cipher that shifts each letter by 3 positions in the alphabet. Our plaintext is “HELLO. Using this cipher:
- H becomes K
- E becomes H
- L becomes O (twice)
- O becomes R
Thus, our ciphertext is “KHOOR.” Only someone who knows the cipher (shift by 3) and the secret key (the number 3) can reverse the process to find the original message.
Visualizing Encryption
If you’re a visual learner, many online resources offer interactive simulations of encryption algorithms. This can be immensely helpful for understanding how mathematical transformations scramble your data.
The Decryption Process
The authorized recipient uses the correct key (and the same algorithm) to unlock the ciphertext:
- The decryption algorithm essentially reverses the steps performed during encryption using the provided key.
- The result, if everything is correct, is the original, readable plaintext message.
Protecting Your Data in the Digital World
Understanding these steps is vital because you may encounter situations where you need to encrypt or decrypt files or messages manually. Popular tools like GPG (GNU Privacy Guard) allow for this kind of individual file encryption.
Real-World Encryption Applications
SSL/TLS and HTTPS
When you see a padlock icon in your browser’s address bar and the website address begins with “https://” you’re witnessing encryption in action! Secure websites rely on SSL/TLS protocols (TLS is the successor to SSL) to encrypt the data flowing between your browser and the website’s server. Let’s break it down:
- Protecting Sensitive Interactions: Think about online forms where you enter personal information, login credentials, or payment data. Encryption ensures that even if an attacker intercepts this traffic, they can’t decipher the content.
- Certificates and Trust: SSL/TLS uses a combination of asymmetric and symmetric cryptography. Digital certificates issued by trusted authorities validate a website’s identity and provide public keys to establish a secure connection.
- Elementor and HTTPS: Modern WordPress installations, by default, tend to use HTTPS. Elementor works seamlessly in this secure environment, and Elementor Hosting offers enhanced security measures like premium SSL certificates to bolster your website’s protection.
Securing Online Forms and Transactions with Elementor
Elementor’s robust form builder is a key tool for collecting data on your website. Here’s how encryption plays a role:
- Forms and HTTPS: Ensuring your website uses HTTPS is the first step in securing form submissions. This encrypts the data in transit between the user’s browser and your website.
- Field-Level Encryption (With Caution): Some third-party plugins can encrypt individual form fields before data even reaches the WordPress database. However, use this feature selectively – it can impact search functionality within the site.
- Payment Gateways: When accepting online payments, consider integrating with reputable payment gateways that prioritize security. Elementor supports popular options like Stripe and PayPal, which handle sensitive financial data with strict encryption standards.
Encrypting Website Data in Transit
It’s important to remember that encryption protects not only form submissions but all data sent to and from your WordPress website while a user is browsing. This includes login attempts, images, text content, and more. This is why enforcing HTTPS on your site is crucial.
Data Storage
Full-Disk Encryption
When it comes to protecting the data residing on your computer’s hard drive or your website’s files on a server, full-disk encryption (FDE) is a powerhouse. Here’s how it works:
- Transparent Encryption: FDE software or hardware encrypts all the contents of a storage device (hard drive, SSD, etc.). To the user, it’s seamless – you access files as usual, with encryption and decryption happening behind the scenes.
- Protection Against Theft: If your laptop or even a server is stolen, FDE renders the data on the drive inaccessible without the decryption key.
- Software vs. Hardware: FDE can be implemented in software (like BitLocker for Windows or FileVault for macOS) or through dedicated hardware on a drive or at the system level. Hardware-based FDE often offers better performance and stronger tamper resistance.
File and Folder Encryption
For a more granular approach, you can encrypt individual files or folders:
- Tools & Utilities: Many operating systems have built-in utilities for this (e.g., Windows Encrypting File System). Additionally, specialized file encryption software provides extra features and flexibility.
- Cloud Storage: Services like Boxcryptor or NordLocker can add a layer of encryption on top of cloud storage providers like Dropbox or Google Drive for enhanced security.
Database Encryption for Sensitive Information within WordPress
Your WordPress database stores a wealth of potentially sensitive information:
- User Data: Depending on your website’s features, this may include customer details, contact forms, account information, etc.
- Content: In some cases, you should protect the content of posts and pages themselves.
- Plugins for Selective Encryption: WordPress plugins can encrypt specific database fields. This targeted approach maintains searchability for non-sensitive data while protecting what matters most.
Elementor Hosting and Data Security
Elementor Hosting places a strong emphasis on protecting your website’s data. Its infrastructure features:
- Server-Side Encryption: Encryption at rest can be an important part of layered security, depending on the nature of the data being stored on your website.
- Robust Security Measures: Firewalls, malware protection, and intrusion detection systems all work in conjunction with encryption to safeguard your website’s data.
Communication
Email Encryption
Email, while an incredibly useful tool, was not designed with inherent security in mind. Encryption offers ways to keep your email correspondence private:
- PGP (Pretty Good Privacy): Popular for personal email encryption, PGP uses asymmetric cryptography. Users exchange public keys to encrypt messages that only the intended recipient’s private key can decrypt.
- S/MIME (Secure/Multipurpose Internet Mail Extensions): Often used in corporate environments, S/MIME also relies on public-key cryptography and digital certificates for email encryption and digital signatures (to verify the sender’s identity).
Secure Messaging Protocols
Instant messaging and chat applications have revolutionized how we communicate. Here’s where encryption makes a big difference:
- Signal: This open-source app employs the robust Signal Protocol for end-to-end encryption. Not even Signal itself can access your messages’ content. It offers secure voice and video calls as well.
- Other Encrypted Messaging Apps: WhatsApp, Telegram (with optional secret chats), and many others offer varying levels of encryption for your conversations.
Protecting Conversations on Your Website
Features like live chat on your website require encryption as potentially sensitive information may be exchanged between you and your customers. When selecting live chat plugins, look for those that prioritize encryption to safeguard these interactions.
Elementor’s Commitment to Communication Security
While not its primary focus, Elementor is designed with security best practices in mind. If you integrate third-party communication features into your Elementor-built website, be sure to research and choose providers that prioritize strong encryption and data privacy policies.
Emerging Technologies
Blockchain’s Use of Cryptography and Hashing
Blockchain, the technology behind cryptocurrencies, relies heavily on strong cryptographic principles:
- Hashing for Immutability: Each block in a blockchain is linked to the previous one using its hash. Any attempt to tamper with data in a block would invalidate the hash, breaking the chain.
- Digital Signatures: Cryptographic signatures verify transactions on blockchains and help ensure the authenticity of the data.
Homomorphic Encryption
Homophic encryption is a fascinating emerging field that allows computations to be performed directly on encrypted data. This could unlock possibilities like secure cloud-based operations on sensitive information without needing to decrypt it first, further enhancing data privacy.
Encryption Best Practices
Strong Encryption Standards
- Stick to Approved Algorithms: Use well-vetted and widely recommended algorithms like:
- AES (for symmetric encryption)
- RSA or ECC (for asymmetric encryption)
- SHA-256 or SHA-3 (for hashing)
- Avoid the Outdated: Algorithms like MD5, DES, and older versions of SHA are known to have vulnerabilities. Avoid them for critical applications.
- Future-Proofing: Keep updated on the latest cryptographic developments, as new attacks and advancements can render older algorithms less secure.
Password Management
Passwords are often the weakest link in encryption systems. Let’s reinforce them:
- Password Managers: These tools help you generate and store strong, unique passwords for every website and service you use.
- Strong Password Characteristics: Aim for length over complexity. Modern guidance emphasizes longer passphrases (think random sentences) over convoluted character combinations.
- Two-Factor Authentication (2FA): Where available, add an extra layer of protection using 2FA, which requires a temporary code or biometric authentication on top of your password.
- Salting and Hashing
Responsible websites and services never store your passwords in plain text. They should use:
- Salting: Adding random data to your password before hashing makes it harder for attackers to crack passwords that users may have reused on other sites.
- Hashing with Iterations: Slowing down the hashing process with multiple rounds makes it much more difficult for brute-force attacks to succeed.
Elementor Password Security
Elementor takes account security seriously. Your Elementor account password is protected with hashing and salting techniques, providing a robust defense against password cracking.
Secure Key Management
- Key Generation: Utilize secure random number generators for key creation. Avoid predictable patterns or keys derived from easily guessed information.
- Key Storage: Choose storage methods appropriate to sensitivity:
- Password managers for individual keys
- Hardware security modules (HSMs) for highly sensitive scenarios
- Key Rotation: Periodically changing keys reduces the impact of a single key being compromised.
- Strict Access Controls: Limit the number of people with access to encryption keys, adhering to the principle of least privilege.
Security Audits & Compliance
- Vulnerability Testing: Engage in routine security audits to identify and patch any weaknesses in your encryption implementations.
- Compliance: Depending on your industry, you may need to adhere to regulations like GDPR (General Data Protection Regulation) or CCPA (California Consumer Privacy Act). Encryption often plays a key role in compliance.
Encryption for Website Owners
Web Hosting Considerations
Your choice of web hosting provider has a profound impact on your website’s encryption landscape:
Benefits of Elementor Hosting:
- Secure Infrastructure: Elementor Hosting leverages Google Cloud Platform’s C2 servers and Cloudflare’s Enterprise CDN, bolstering your security with robust technologies
- Premium SSL Certificates: SSL/TLS is essential for HTTPS, and Elementor Hosting includes enhanced SSL Certificates for your website.
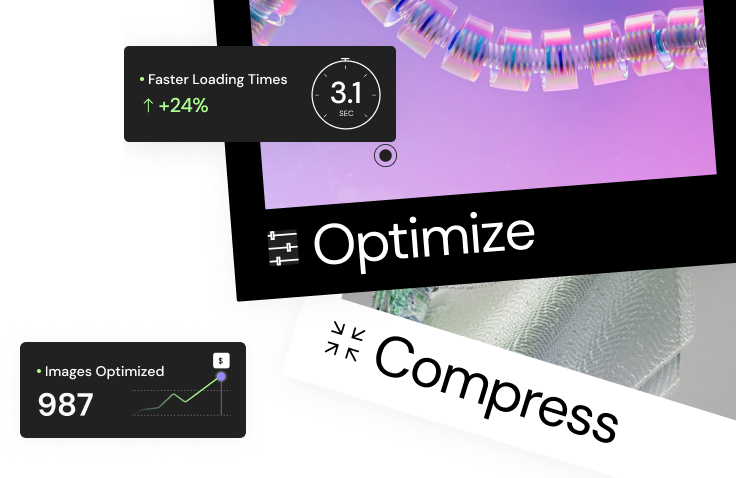
- Performance Optimization: Speed optimizations, which are integrated into Elementor Hosting, can indirectly improve security by reducing vulnerability windows and mitigating certain attack types.
Server-Side vs. Client-Side Encryption:
- Server-side encryption happens on the web server itself, protecting data in transit and at rest. Your hosting provider plays a significant role in server-side encryption.
- Client-side encryption occurs within the user’s browser using JavaScript. This is useful for adding an extra layer of protection for highly sensitive data.
Implementing Encryption in WordPress
- Enforcing HTTPS: A non-negotiable first step. Utilize your hosting control panel tools or WordPress plugins to redirect all traffic to the secure HTTPS version of your website.
- Encryption Plugins (Use with Care): Plugins may offer features like field-level encryption for forms or database entries. However, choose these plugins wisely as they can impact performance and may have other implications for your website’s functionality (e.g., affecting internal search).
- Third-Party Services: If using external payment gateways, form providers, or communication tools, prioritize providers that transparently explain their encryption and security practices.
Securing User Data with Elementor Forms
- HTTPS: As always, forms submitted over HTTPS are automatically protected by transport encryption, ensuring data privacy in transit.
- Privacy Regulations: If handling personal data, understand regulations like GDPR, paying special attention to consent requirements and the need for potential encryption.
- Elementor Form Security Features: While not its core focus, Elementor Forms include elements like honeypots and reCAPTCHAs to help mitigate spam and bot attacks.
Protecting Sensitive Content
- WordPress Security Approach: For baseline protection, always follow WordPress security best practices (strong passwords, software updates, reputable plugins).
- Membership Plugins: If restricting access to content is necessary, select plugins that emphasize security in their design.
- Selective Encryption: In specialized cases, WordPress plugins may allow you to encrypt individual posts or pages for enhanced privacy.
Staying Secure
The Importance of WordPress and Elementor Updates
Keeping WordPress, Elementor, and any plugins you use up-to-date is one of the most effective ways to secure your website. Why?
- Patching Vulnerabilities: Security updates often address newly discovered security flaws. Refrain from affecting updates leaves your site exposed to known attacks.
- Keeping Pace with Evolving Threats Security teams behind WordPress and Elementor constantly work to improve encryption implementations and counter evolving threats.
Elementor’s Commitment to Updates
Elementor maintains a regular release cycle with both feature updates and important security patches. When managing your site, be sure to apply these updates as they become available to keep your Elementor installation secure.
Website Security Tools & Monitoring
- Firewall Solutions: Web Application Firewalls (WAFs) like the kind included with Elementor Hosting offer protection against common web attacks like SQL injections and cross-site scripting (XSS).
- Malware Scanning: Regularly scan your website files for malware infections. Many hosting providers offer malware scanning tools, or you can utilize dedicated security plugins.
- Intrusion Detection: Monitoring your website for unauthorized access or suspicious activity can help you uncover security incidents early and respond quickly.
- Security Audits: Periodically conduct thorough security audits of your website, especially if you handle sensitive data. Engaging professional security experts can be beneficial for in-depth assessments.
Website Security Best Practices
Let’s reinforce your security knowledge with key practices for any WordPress website owner:
- Strong Passwords and Account Security: Enforce secure passwords on your WordPress admin area, hosting account, and anywhere related to your site’s infrastructure.
- User Permissions: Follow the principle of least privilege. Grant users only the minimum permissions they need to perform their roles on your site.
- Backups: Have a robust backup solution with both on-site and off-site copies. This is your lifeline in case of a serious security compromise.
- Reputable Plugins and Themes: Before installing plugins and themes, choose carefully, researching their track record and security history.
- Monitoring and Incident Response: Pay attention to logs and security alerts, and have a plan in place for how you’ll respond to potential security breaches.
The Future of Encryption
Quantum Computing Challenges
One of the most significant potential disruptors to traditional encryption is quantum computing. Quantum computers harness principles of quantum mechanics to perform calculations that are currently intractable for classical computers.
- The Threat to Encryption: Some cryptographic algorithms that are secure today could be broken by sufficiently powerful quantum computers. This includes widely used RSA encryption, putting sensitive data at risk in the long term.
The Development of Quantum-Resistant Cryptography
The good news is that cryptographers are already working to counter this threat:
- New Algorithms: Researchers are developing encryption algorithms that are believed to be resistant to attacks even by quantum computers.
- Standardization and Migration: A gradual but crucial task is standardizing these new algorithms and transitioning existing systems to adopt them before quantum computers become a practical threat.
The Role of Governments and Organizations
Governments, tech giants, and standards bodies are actively involved in the race for quantum-resistant encryption:
- NIST: The National Institute of Standards and Technology (NIST) is spearheading a collaborative effort to select and standardize new quantum-resistant algorithms.
- Staying Updated: Website owners need to be aware of these developments. While the immediate threat is small, future-proofing websites for the quantum era may involve adopting new encryption standards over time.
Additional Future Directions
Aside from quantum computing, here are a few other trends in the encryption world:
- Further Advancements in Homomorphic Encryption: If practical limitations can be overcome, homomorphic encryption has immense potential to enhance privacy in cloud computing and other scenarios.
- Increased Focus on Usability: Making encryption easy and seamless for end-users is a constant goal to encourage adoption and decrease human error vulnerabilities.
Conclusion
Key Takeaways
As you’ve seen, encryption plays a vital role in cybersecurity, protecting everything from personal emails to sensitive corporate and government data. Here’s a recap of what we’ve learned:
- The Basics: Encryption transforms data into unreadable ciphertext, decipherable only with the correct key.
- Applications Abound: Securing websites, online transactions, data storage, communication, and much more.
- Always Advancing: Encryption must continue to evolve to counteract emerging threats like quantum computing.
- Security Is a Journey: Best practices, vigilance with updates, and employing encryption wisely are all keys to a proactive security stance.
Encryption and Your WordPress Website
By choosing a trusted hosting partner like Elementor Hosting and following the strategies outlined in this guide, you can greatly enhance the security of your WordPress website.
I believe this comprehensive article provides a valuable foundation for anyone seeking to understand the importance of encryption and how to utilize it effectively in the modern digital age.
Looking for fresh content?
By entering your email, you agree to receive Elementor emails, including marketing emails,
and agree to our Terms & Conditions and Privacy Policy.